Windows Server Update 2025: Everything You Need to Know Windows Server 2025, released on November 1, 2024, represents Microsoft's most significant server update in years, introducing groundbreaking features like hotpatching, advanced AI capabilities, and enhanced...
Blog
Home / Blog

AlmaLinux vs Rocky Linux 2025: Full Comparison & Best Choice 🔥
AlmaLinux vs Rocky Linux 2025: Full Comparison & Best Choice 🔥 Both AlmaLinux and Rocky Linux emerged as leading CentOS replacements, offering enterprise-grade Linux distributions with 10-year support lifecycles and RHEL compatibility. While they share many...
The Best Ad Blockers for 2026 – Complete Guide & Reviews
The Best Ad Blockers for 2026 Online advertising has become increasingly intrusive, with trackers following your every move across the internet and ads disrupting your browsing experience. Ad blockers not only remove annoying advertisements but also protect your...
Top 5 Best Linux Distro (2026): Beginner to Power User
Top 5 Best Linux Distro (2026): Expert Guide for Every User When evaluating the top 5 best Linux distro options available in 2026, several critical factors come into play that make Linux an increasingly dominant choice for desktops, servers, laptops, and even embedded...
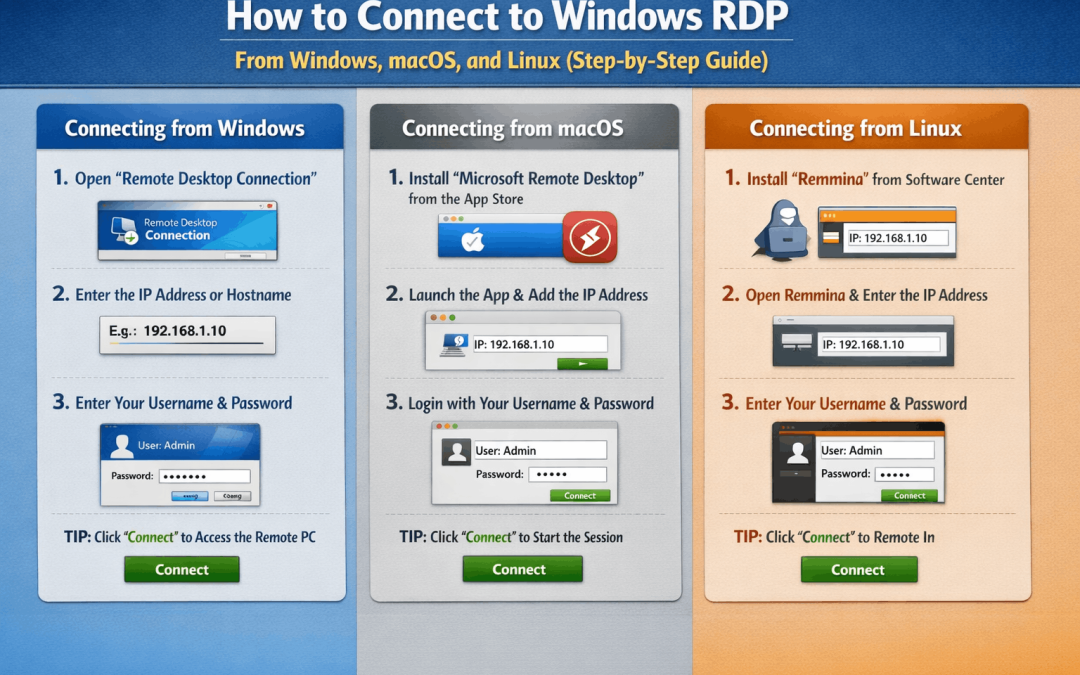
Connect to Windows RDP: 3 Easy Ways from Windows, macOS, and Linux (Step‑by‑Step)
How to connect to Windows RDP from Windows, macOS, and Linux Remote Desktop Protocol (RDP) lets you see and control a Windows PC or server from another device as if you were sitting in front of it. This guide shows how to connect to Windows RDP from Windows, macOS,...
RDP Session Security: Disable Clipboard and Drive Redirection Safely
RDP session security: why clipboard and drive redirection are risky RDP session security is only as strong as the paths data can use to leave your servers. Clipboard, drive, and device redirection are convenient, but they quietly create high‑risk channels between the...
RDP Brute Force Protection: How to Detect and Block Attacks in Windows
RDP brute force protection: how to detect and block attacks RDP brute force protection is essential because RDP brute-force attacks remain one of the most common entry points for ransomware and full server takeovers. With a few practical steps, you can detect these...
Expose RDP: 7 Critical Risks (and the Safest Alternatives)
Expose RDP: 7 Critical Risks (and the Safest Alternatives) Remote Desktop Protocol (RDP) is convenient, but putting it directly on the public internet is one of the most common ways Windows servers get attacked. Attackers constantly scan the internet for RDP services,...
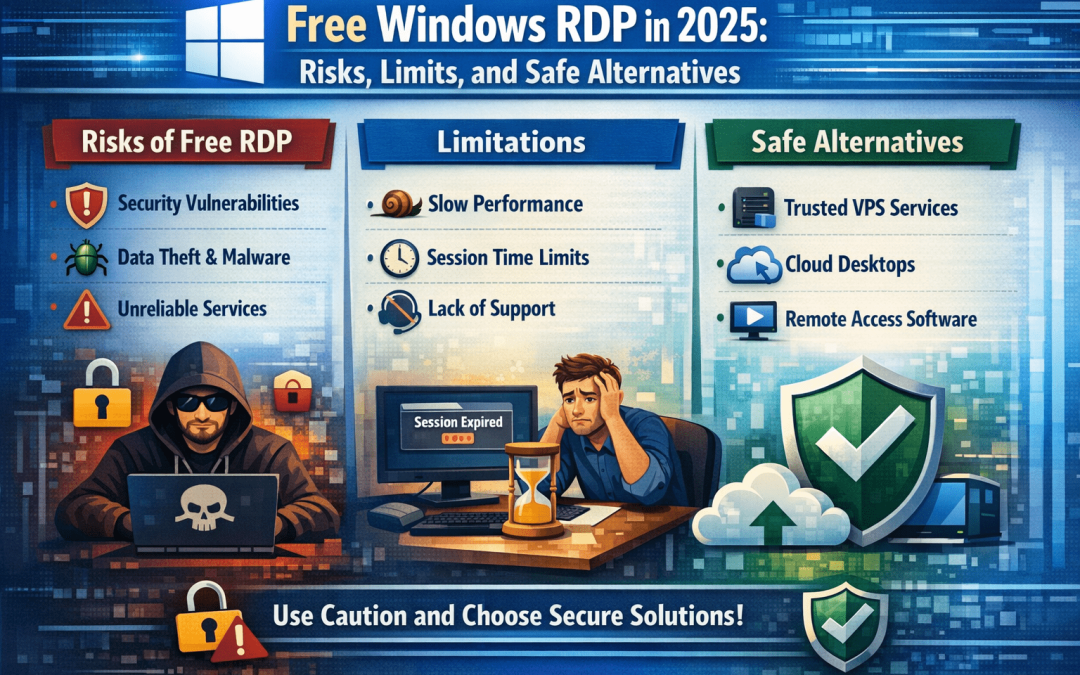
Free Windows RDP in 2025: Risks, Limits and Safe Alternatives
Free Windows RDP in 2025: Risks, Limits, and Safe Alternatives If you’re evaluating Free Windows RDP in 2025, treat it like any other untrusted compute resource on the internet: assume hostile tenancy, unknown provenance, and zero assurance on patch level, identity...
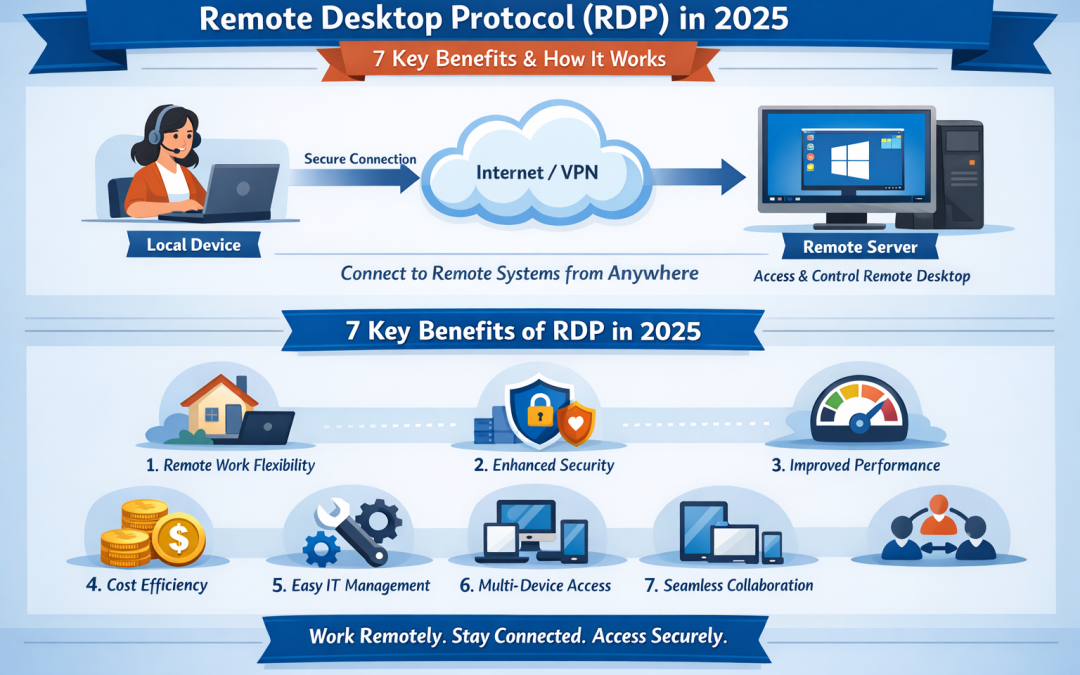
Remote Desktop Protocol (RDP): 7 Key Benefits & How It Works in 2025
Remote Desktop Protocol (RDP): 7 Key Benefits & How It Works in 2025 Remote Desktop Protocol (RDP) is a Microsoft-developed technology that allows users to remotely access and control a Windows computer or server over the internet. With Remote Desktop Protocol,...

